SMS Fraud Guide: How It Works, How It Spreads, and How to Stop It
There’s a particular kind of silence that shows up in messaging systems when something isn’t right. Traffic looks healthy, throughput is stable. Dashboards don’t raise alarms.
There’s a particular kind of silence that shows up in messaging systems when something isn’t right. Traffic looks healthy, throughput is stable. Dashboards don’t raise alarms. And yet, revenue starts slipping in ways that don’t quite add up. Delivery reports remain “successful,” but downstream outcomes, user actions, conversions, and OTP validations begin to drift.
 If you’ve operated messaging infrastructure long enough, you learn to distrust clean-looking traffic. Because SMS fraud rarely announces itself as a spike, it blends in. It borrows the shape of legitimate traffic and moves through the same pipes. And by the time it’s obvious, the damage has already settled into your margins. That’s why SMS fraud isn’t just a security concern anymore, it’s an operational one.
If you’ve operated messaging infrastructure long enough, you learn to distrust clean-looking traffic. Because SMS fraud rarely announces itself as a spike, it blends in. It borrows the shape of legitimate traffic and moves through the same pipes. And by the time it’s obvious, the damage has already settled into your margins. That’s why SMS fraud isn’t just a security concern anymore, it’s an operational one.
What SMS Fraud Actually Looks Like in a Live Network
From the outside, SMS fraud is often reduced to a few familiar ideas, spam campaigns, phishing attempts, and unauthorized traffic. That framing is too narrow, inside a live network, SMS fraud is less about content and more about traffic manipulation.
It shows up as messages taking unexpected paths. Routes that shouldn’t carry traffic suddenly do. Margins compress without any change in pricing agreements. Delivery remains technically “successful,” but the economic logic behind it breaks.
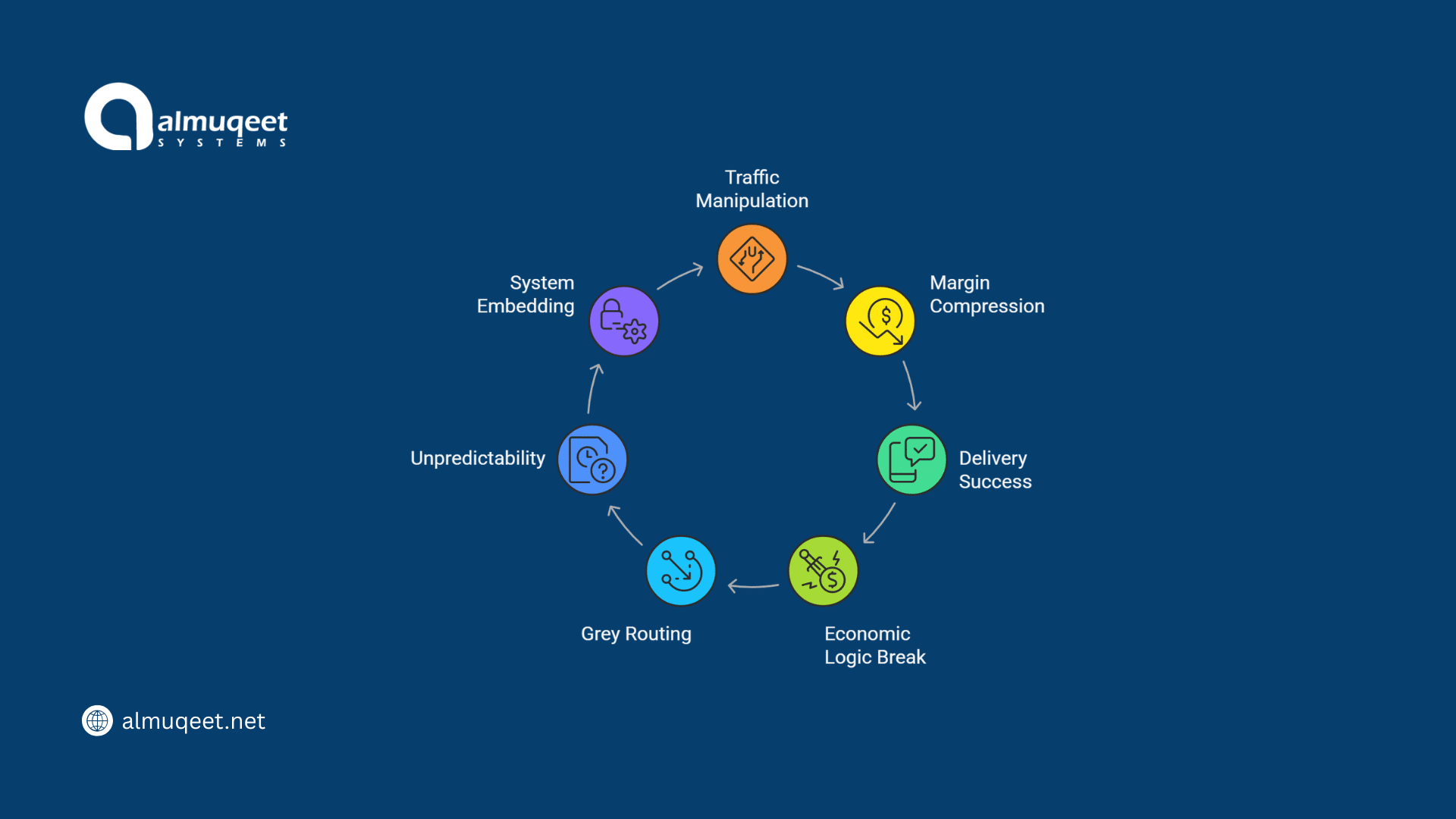 A common pattern is grey routing messages, bypassing official channels to reduce costs. It sounds like an optimization until you realize what it introduces, unpredictability. Messages may still reach users, but not consistently, and not always within the time windows your applications depend on. Over time, these behaviors stop being edge cases. They become embedded in the system.
A common pattern is grey routing messages, bypassing official channels to reduce costs. It sounds like an optimization until you realize what it introduces, unpredictability. Messages may still reach users, but not consistently, and not always within the time windows your applications depend on. Over time, these behaviors stop being edge cases. They become embedded in the system.
How SMS Fraud Spreads Without Being Noticed
Fraud in messaging doesn’t spread like an attack. It spreads like a workaround, it starts with one route that performs slightly better under cost pressure. Maybe it’s cheaper. Maybe it avoids a regulatory bottleneck. Maybe it just delivers faster under certain conditions.
Then traffic shifts gradually, then aggressively. The problem is that most systems don’t reevaluate routing decisions continuously. They optimize once, then assume stability. But telecom environments don’t stay stable. Operators change filtering rules. Networks rebalance capacity. Compliance frameworks evolve.
What worked last month quietly becomes a liability. And because fraud often operates inside those “working” routes, it inherits legitimacy. It doesn’t trigger alarms because, technically, nothing is broken. This is where the boundary between optimization and fraud becomes difficult to see.
When SMS Fraud Stops Being a Risk and Becomes Infrastructure Debt
Early on, teams treat SMS fraud as something external, and bad actors are exploiting the system. At scale, that distinction fades. Because once fraudulent routes or behaviors are embedded into your traffic flow, removing them isn’t just a security fix. It’s a system redesign.
We’ve seen environments where blocking a single grey route caused delivery rates to drop overnight. Not because the route was good but because the system had quietly become dependent on it. That’s the shift. Fraud stops being a threat you defend against and becomes a dependency you have to unwind carefully, and that’s never quick.
A Real Scenario: When “Delivered” Isn’t Good Enough
Consider a logistics platform sending delivery updates and OTP confirmations across multiple regions. On paper, everything works. Messages are being sent. Delivery receipts come back as successful, no obvious failure. But customer complaints start increasing. Drivers aren’t receiving updates on time. OTPs arrive after the verification window expires. Support teams begin escalating issues that don’t show up in system logs.
After digging deeper, the issue surfaces: a portion of traffic is being routed through low-cost grey paths. These routes deliver eventually. But not reliably. And not within the time sensitivity the system assumes. From a reporting perspective, the system is “healthy.”From a user perspective, it’s broken. That gap is where SMS fraud does its most damage.
Why Traditional Detection Methods Fall Short
Most fraud detection systems are built around visibility patterns, anomalies, and spikes. The problem is that modern SMS fraud doesn’t behave like an anomaly. It behaves like normal traffic with slightly different economics.
There are a few signals operators tend to watch:
- Sudden changes in delivery patterns
- Unusual routing distributions
- Margin inconsistencies across similar traffic
- Increased latency without network congestion
But none of these are definitive on their own. They require context. And context is often fragmented across systems, routing engines, billing platforms, and delivery reports. This is why SMS fraud detection often lags behind its impact. You don’t catch it when it starts. You catch it when the numbers stop making sense.
The Role of Infrastructure in Containing SMS Fraud
There’s a tendency to look for a single solution, usually framed as a firewall or detection layer. That helps, but it’s not enough on its own. Containing SMS fraud is less about blocking traffic and more about controlling how traffic is allowed to move through your system.
At a practical level, this means tightening a few key areas:
- Routing discipline: ensuring traffic follows verified, intentional paths
- Real-time number intelligence: validating where messages should actually be delivered (this is where systems using accurate lookup layers tend to outperform static routing assumptions)
- Traffic visibility: not just volume, but economic behavior
- Fallback logic: avoiding silent degradation when routes fail
If you’ve worked through how routing decisions change when number intelligence is introduced, it becomes clear that fraud often thrives in the gaps between outdated assumptions and real-time network conditions, that’s not accidental.
Where SMS Fraud Hits Hardest
Not every use case feels SMS fraud the same way. In marketing campaigns, delays are inconvenient. In transactional systems, they’re critical.
Industries where timing and reliability matter most tend to feel the impact first:
- Fintech: OTP delays directly affect authentication and trust
- Logistics: real-time updates lose value if they arrive late
- Healthcare: appointment reminders and alerts depend on timing
- E-commerce: order confirmations and delivery notifications shape customer experience
The common thread is expectation. Users don’t think in terms of delivery rates. They think in terms of whether the message arrived when it mattered. SMS fraud disrupts that quietly.
Stopping SMS Fraud Without Breaking the System
There’s no clean switch you can flip to eliminate SMS fraud. The systems are too interconnected for that. What tends to work over time is a combination of control and awareness:
- Gradually tightening routing policies instead of abrupt changes
- Introducing real-time validation layers where timing matters most
- Monitoring economic signals, not just delivery metrics
- Accepting short-term performance trade-offs to remove long-term risk
It’s rarely a perfect transition. There are always moments where delivery dips, costs increase, or routes need to be rebuilt. But that’s the nature of moving from opportunistic routing to controlled infrastructure.
The Quiet Reality of SMS Fraud in 2026
Messaging has become too critical to treat fraud as an edge problem. Traffic volumes are higher. User expectations are tighter. Regulatory pressure is more consistent across regions. But the biggest change is subtle: messaging systems are now part of the core product experience. That means the cost of inconsistency, whether caused by fraud, routing errors, or latency, is no longer isolated. It shows up in churn, in failed transactions, in lost trust. SMS fraud doesn’t break systems loudly. It bends them slowly. And unless you’re looking closely, it’s easy to mistake that bend for normal behavior.
A Final Thought on Control
Most messaging systems start with flexibility. Routes are added quickly. Costs are optimized aggressively. Traffic flows where it can. That works until it doesn’t. At some point, every system has to decide whether it wants to remain flexible or become reliable. And that usually means reducing the degrees of freedom that fraud depends on. Not all at once but deliberately. Because the goal isn’t to eliminate complexity. It’s to make sure complexity doesn’t control your outcomes.
FAQs
1. How is SMS fraud different from spam or phishing?
Spam and phishing are content-driven issues. SMS fraud is infrastructure-driven. It often involves how messages are routed, billed, or manipulated within the network rather than what the message contains.
2. Can SMS fraud exist even if delivery reports show success?
Yes. Delivery reports indicate that a message reached the network endpoint, not that it arrived reliably or within the expected time frame. Fraud often hides within “successful” delivery.
3. Is grey routing always considered SMS fraud?
Not always, but it’s a common channel for fraud. Grey routes bypass official agreements, which introduces risk in delivery consistency, compliance, and revenue tracking.
4. What’s the first sign that SMS fraud might be affecting a system?
Often, it’s subtle margin inconsistencies, unexplained delivery delays, or performance differences across similar traffic segments.
5. Do SMS firewalls eliminate fraud?
They reduce exposure significantly, especially at the network edge. But fraud can still exist within routing logic and traffic behavior, which requires broader system-level controls.
6. How can teams reduce SMS fraud without impacting delivery rates?
By introducing changes gradually, validating routes, adding intelligence layers where necessary, and monitoring both delivery and economic signals rather than focusing on one metric alone.
Share this post