The first sign is almost always a billing report, not an alert, not a dashboard going red, and not a security ticket. A finance person, sometimes around the 3rd or 4th of the month, walks over and asks why the SMS spend is up 40% when nothing else has changed. No new product launch, no marketing push, no campaign that would explain it. Just a number that doesn’t sit right. That’s usually the moment a messaging team realises quietly, internally, that something has been wrong for weeks.
 This is what artificial inflation traffic looks like in real life, not a dramatic breach, not an alert in red. Just a slow, expensive bleed that hides inside numbers everyone trusted. And the harder truth is that artificial inflation traffic rarely announces itself, it builds inside legitimate-looking OTP and signup flows, gets billed as normal A2P volume, and only becomes obvious once the invoice lands. For most operators and enterprises, that’s already too late.
This is what artificial inflation traffic looks like in real life, not a dramatic breach, not an alert in red. Just a slow, expensive bleed that hides inside numbers everyone trusted. And the harder truth is that artificial inflation traffic rarely announces itself, it builds inside legitimate-looking OTP and signup flows, gets billed as normal A2P volume, and only becomes obvious once the invoice lands. For most operators and enterprises, that’s already too late.
Why AIT Fraud Slips Past Every Filter You Have
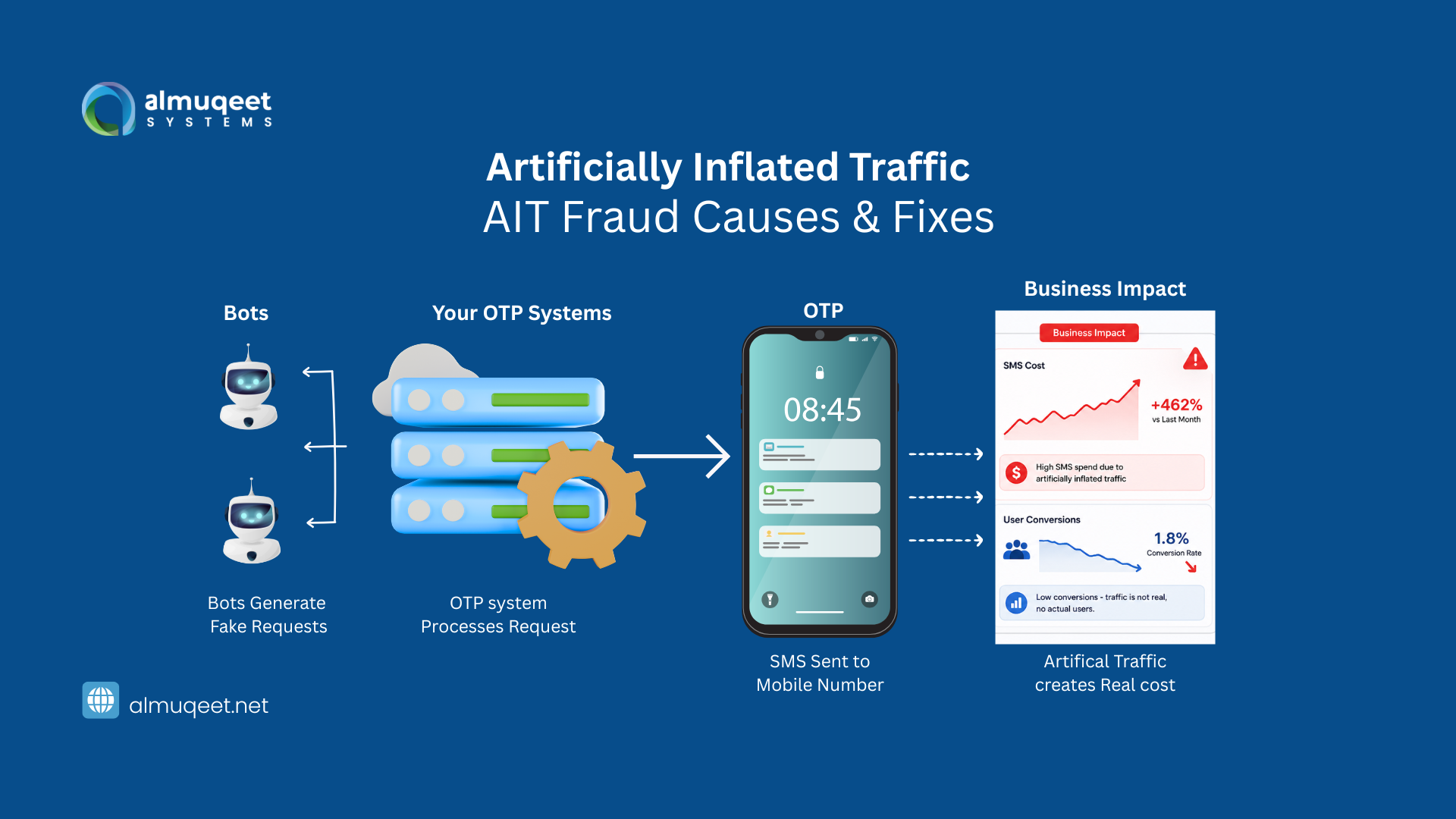
Forget the textbook framing, AIT, sometimes called SMS pumping, sometimes OTP pumping, when it specifically targets verification flows, is a coordinated abuse of your OTP and signup endpoints, where bots generate massive volumes of SMS sends to a small set of premium-rate or revenue-share-friendly destinations.
The attacker doesn’t care about reading your OTP, they never log in. They don’t even need to receive the message in any meaningful way. The whole point is for the message to be sent and billed, because somewhere downstream through a chain of routing partners and termination agreements, a portion of that termination revenue ends up in the attacker’s pocket.
So you pay for the SMS, and the aggregator gets paid. The operator on the receiving end gets paid. And whoever sits at the end of that chain, sometimes a complicit MNO in a small market, sometimes a SIM-farm operator using number ranges they control, pockets the share. You’re not being hacked. You’re being used as a payment rail.
What Artificial Inflated Traffic Actually Looks Like Inside the Network
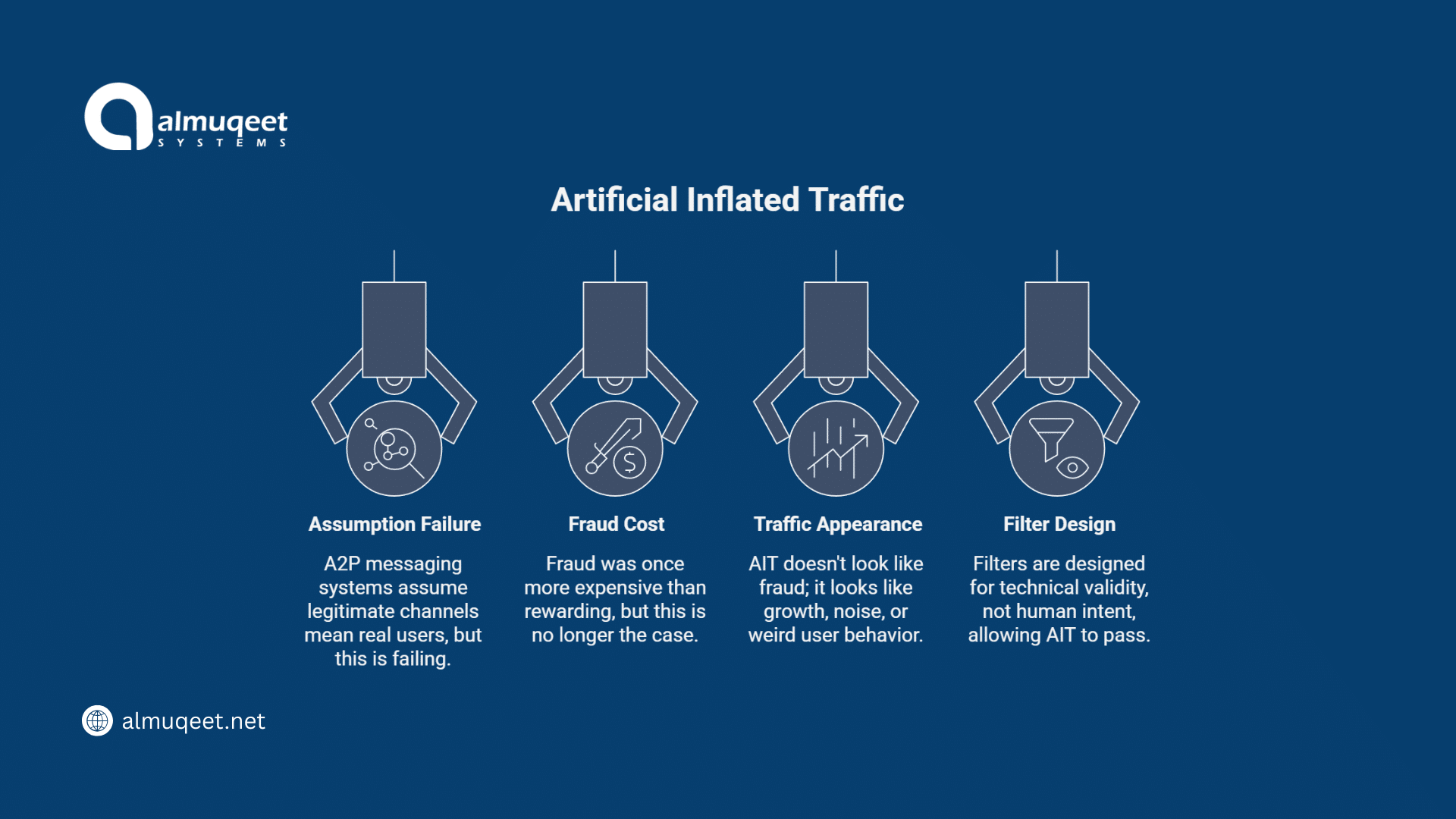
A2P messaging systems are built on an assumption that’s been quietly failing for years: that if a request comes through a legitimate channel, your signup form, your login screen, your password-reset endpoint, it’s coming from a real user with real intent.
For most of A2P’s history, that assumption held. The cost of fraud was higher than the reward. Spinning up enough fake numbers to matter required infrastructure most attackers didn’t bother with. That’s no longer true, and the gap between “no longer true” and “operators have updated their systems” is where AIT lives.
How an SMS Pumping Attack Really Unfolds
If you’ve watched it happen in real time, and more and more teams have adopted the pattern, it is depressingly clean. It starts with a bot finding your OTP endpoint. This isn’t difficult. Any signup form, any “verify your phone number” flow, any forgot-password journey is a candidate. The bot doesn’t need to be sophisticated. It needs to be patient.
Phase one is usually quiet: A few hundred requests, scattered across countries, are designed to test what your system actually validates.
- Does your form accept any MSISDN format?
- Does it rate-limit by IP? By number? By session?
- Does it block obviously invalid prefixes? Most don’t.
Phase two is targeting: The bot identifies which destination ranges trigger the highest-cost routes, typically obscure number ranges in markets with high termination fees and weak oversight. Those are the goldmines.
Phase three is scale: Suddenly, you’re sending tens of thousands of OTPs to numbers in three or four specific country-prefix combinations. From your side, the traffic looks like a marketing surge in an emerging market. You might even feel quietly pleased about international growth.
By the time someone notices the conversion rate from those new “users” is zero, because none of them is users, the bill has already been generated.
Why OTP Fraud and AIT Work So Well Against Modern A2P Systems
The honest answer is that A2P infrastructure was never designed with this threat model in mind. Most platforms enforce delivery, not legitimacy. The validation layer ends at “is this a real number that can receive an SMS?” and AIT exploits the fact that yes, it absolutely is, and yes, it absolutely can.
The deeper problem is layered:
Rate-limiting is usually too coarse. Limits per IP are easily defeated by rotating proxies. Limits per phone number don’t help when attackers control thousands of valid numbers. Limits per session are bypassed by simply opening more sessions.
Number intelligence, knowing whether a destination is a regular subscriber, a recently-ported range, a known SIM-farm prefix, or a high-risk corridor, is often missing entirely from the OTP flow. The form accepts anything that looks like a phone number.
Real-time filtering on the messaging side rarely sees enough context. The SMSC sees a valid request from a trusted enterprise customer; it has no business asking why.
And finally, there’s the trust assumption itself. OTP flows are treated as low-risk because each individual OTP is low-value. Nobody designed those flows assuming someone would request a million of them.
The Hidden Damage of AIT Fraud Goes Far Beyond the Bill
The cost line on the invoice is the obvious wound. It’s also the smallest one, in many cases. Your CRM ends up filled with thousands of half-completed signups that will never convert. Your conversion-rate dashboards quietly poison themselves. Marketing decisions get made on the back of “user growth” that doesn’t exist. Product teams chase activation problems that aren’t activation problems.
On the routing side, your SMS provider sees a sudden surge of traffic to unusual corridors and starts adjusting your routing profile to handle it. Now your legitimate traffic to those countries is travelling through routes optimised for the volume of fake traffic, and your delivery rates start drifting.
If your fraud is loud enough, downstream operators may start blocking your sender IDs, treating you as a polluted source. That damage outlasts the attack. And then there’s the operational tax: the post-mortems, the painful negotiations with aggregators about which charges should be reversed, the emergency meetings, the trust hit with finance leadership. None of that shows up in the invoice either.
Why Most Operators Still Haven’t Patched the SMS Pumping Problem
This is the part that’s frustrating to talk about, because the answer isn’t technical, it’s structural. A lot of telcos and aggregators still treat A2P messaging as a delivery business. The KPIs are built around throughput, latency, and DLR success. Fraud sits in a different team, usually a signalling-security team focused on SS7 and SIGTRAN, and AIT doesn’t fit neatly into either domain.
It’s not really a signalling attack; the signalling is fine. The MAP messages are well-formed, and the SS7 firewall has nothing to flag. It’s not really a delivery problem either. The delivery is excellent, that’s the whole point.
So AIT falls into a gap. It looks like a customer behaviour anomaly to the routing team, like a billing irregularity to finance, and like a product-side bot problem to engineering. None of those teams individually owns it, and the tooling each of them uses is blind to the others’ signals.
Add to that the fact that some operators in the chain benefit from AIT, they’re the ones receiving the inflated termination revenue, and you have a problem that’s structurally underweighted across the industry.
Signals Your Traffic Is Already Carrying AIT Fraud
If you’re reading this and wondering whether your own traffic is clean, here are the patterns that tend to surface first:
A sudden, sustained increase in OTP volume to a small number of destination prefixes, with no corresponding growth in active users from those countries. The conversion ratio is the giveaway. Healthy OTP flows convert somewhere in the 70–90% range. AIT-poisoned traffic often sits at single digits.
Repeated OTP requests for the same numbers within short windows, particularly during low-traffic hours in your primary markets. Bots don’t sleep when your users do.
Concentration around specific MCC/MNC pairs you don’t normally see in your user base, and especially around recently-allocated number ranges that don’t correspond to any consumer-grade operator you’d recognise.
Sudden mismatches between requested OTP volume and downstream events: signup completions, login attempts, and password resets actually finished. If the funnel from “OTP sent” to “user did the thing” has collapsed, you’re paying for messages no one wanted.
What Actually Stops Artificially Inflated Traffic Before It Hits Your Invoice
The fix isn’t a single product. It’s a mindset shift, treating the OTP flow as a risk surface, not a delivery pipeline.
The first practical layer: number intelligence at the point of request. Before an OTP is even generated, the destination number should be checked against an HLR or MNP lookup that confirms it’s a live, attached subscriber on a recognised network, not a recently-ported range, not a number sitting in a known SIM-farm prefix, not an MSISDN with anomalies that suggest disposability. This single layer kills a meaningful percentage of AIT before it ever reaches the SMSC.
The second layer: behavioural rate-limiting that works on combinations of signals: IP, number, session, fingerprint, country corridor, and time-of-day pattern. Single-axis limits are bypassable. Multi-axis limits are not.
The third layer: real-time SMS firewall logic that watches the corridor itself. If traffic to a particular MCC/MNC pair triples in 48 hours with no business explanation, that should generate an alert long before finance sees a bill. A modern SMS firewall isn’t just an SS7 gatekeeper anymore; it’s a traffic-pattern observer, and the patterns AIT produces are visible if anyone is actually looking.
The fourth layer: the one most teams skip, post-send conversion analysis. Track the ratio between OTPs sent and OTPs actually used. Per country. Per route. Per sender ID. The moment that ratio starts diverging in a specific corridor, you have your answer.
None of this requires a re-architecture. It requires deciding that messaging traffic is an attack surface and resourcing it as one.
How Almuqeet Helps You Tackle AIT Fraud
At Almuqeet Systems, we treat AIT as what it really is: a direct attack on your messaging budget and your operational integrity. That’s why our infrastructure is built to detect, block, and prevent artificially inflated traffic before it ever reaches your invoice:
- We continuously monitor A2P traffic patterns to flag abnormal OTP volumes, suspicious sender behaviour, and unusual destination spikes and alert clients the moment something looks off.
- We block AIT fraud at both the destination network level and the MSISDN range level, cutting off bot-driven traffic at the source.
- Our HLR Lookup and MNP validation services let you verify every number before an OTP is sent, stopping fake or high-risk numbers from entering your flow in the first place.
- Our SMS firewall inspects traffic in real time, scoring routes and identifying patterns consistent with SMS pumping and OTP fraud.
- We actively maintain a registry of high-risk destinations, grey-route operators, and known fraud-linked number ranges and update it as the threat landscape shifts.
Beyond the tech, we believe a cleaner A2P ecosystem benefits everyone. That’s why our routing strategy excludes operators with poor fraud controls, why we maintain direct carrier relationships wherever possible to keep the trust chain short, and why we work with clients to add AIT-specific clauses into their messaging agreements.
Almuqeet’s mission isn’t just delivering messages. It’s making sure every message you pay for is one your real users actually receive.
AIT Fraud Isn’t Coming. It’s Already in Your Traffic.
AIT isn’t a future threat. It isn’t an emerging concern. It isn’t something to put on next quarter’s roadmap. It’s already running through the traffic of most A2P platforms right now, in volumes nobody has measured precisely because the systems aren’t designed to measure it. The reason it doesn’t show up as fraud in your dashboards is that your dashboards weren’t built to recognise it. Every message is valid. Every route is legitimate. Every charge is technically owed.
The fraud isn’t in any single message. It’s a fact that no human ever wanted any of them. That’s the part operators keep missing, and the part attackers are quietly counting on.
Frequently Asked Questions
How does AIT fraud work?
Bots repeatedly hit a platform’s OTP endpoints using phone numbers tied to specific high-cost routes. The fraud ring earns a share of the SMS termination revenue, while the business pays for messages nobody reads.
How is AIT fraud different from regular SMS fraud or smishing?
They target opposite ends of the messaging chain. Smishing targets the recipient, tricking a real person into clicking a bad link. AIT targets the sender, exploiting the business that pays for the SMS. No victim is receiving the message because no human ever wanted it. That’s also why traditional fraud filters miss it: they’re built to catch suspicious content, not suspicious traffic patterns.
Why is AIT so hard to detect through normal monitoring?
Because every individual signal looks clean, valid IP, real MSISDN, successful delivery, and positive DLR. Nothing in a single transaction screams fraud.
Can HLR or MNP lookup actually stop AIT before it starts?
It can stop a meaningful slice, mostly the less sophisticated attacks. A real-time HLR check at the OTP request filters out numbers that aren’t attached or sit in suspicious prefix ranges.
Who actually profits from AIT fraud?
The money flows backward through the termination chain. When you send an SMS, the receiving operator earns a termination fee. In AIT schemes, the attacker has either struck a revenue-share deal with a complicit downstream party, controls a block of numbers in a high-cost corridor, or sits inside a small operator pocketing a share.
Is AIT mostly a problem for big enterprises, or are smaller businesses also being hit?
Smaller businesses often get hit harder. Large enterprises have fraud teams, real-time monitoring, and leverage to push back on aggregators. A mid-sized SaaS running OTP through a generic CPaaS usually has none of that; they notice the spike weeks later and absorb the loss.
