Messaging networks usually reveal their problems in small ways. Not outages, no alarms, just small signals that something inside the system isn’t behaving the way it should. An authentication code that normally arrives instantly suddenly takes ten seconds. A batch of delivery receipts comes back unevenly. Support teams start hearing the same complaint from different regions: “The message eventually arrived, but it took longer than usual.”
If you’ve spent time around telecom messaging infrastructure, you learn that these patterns rarely happen by accident. Somewhere along the routing path, traffic has started entering the network in ways it shouldn’t, grey routes injecting A2P messages, sender IDs being reused across unrelated campaigns, or external gateways pushing volumes that the operator never authorized. None of this breaks the network outright. Messages still move. Subscribers still receive notifications. But the network quietly loses control over how traffic enters and behaves.
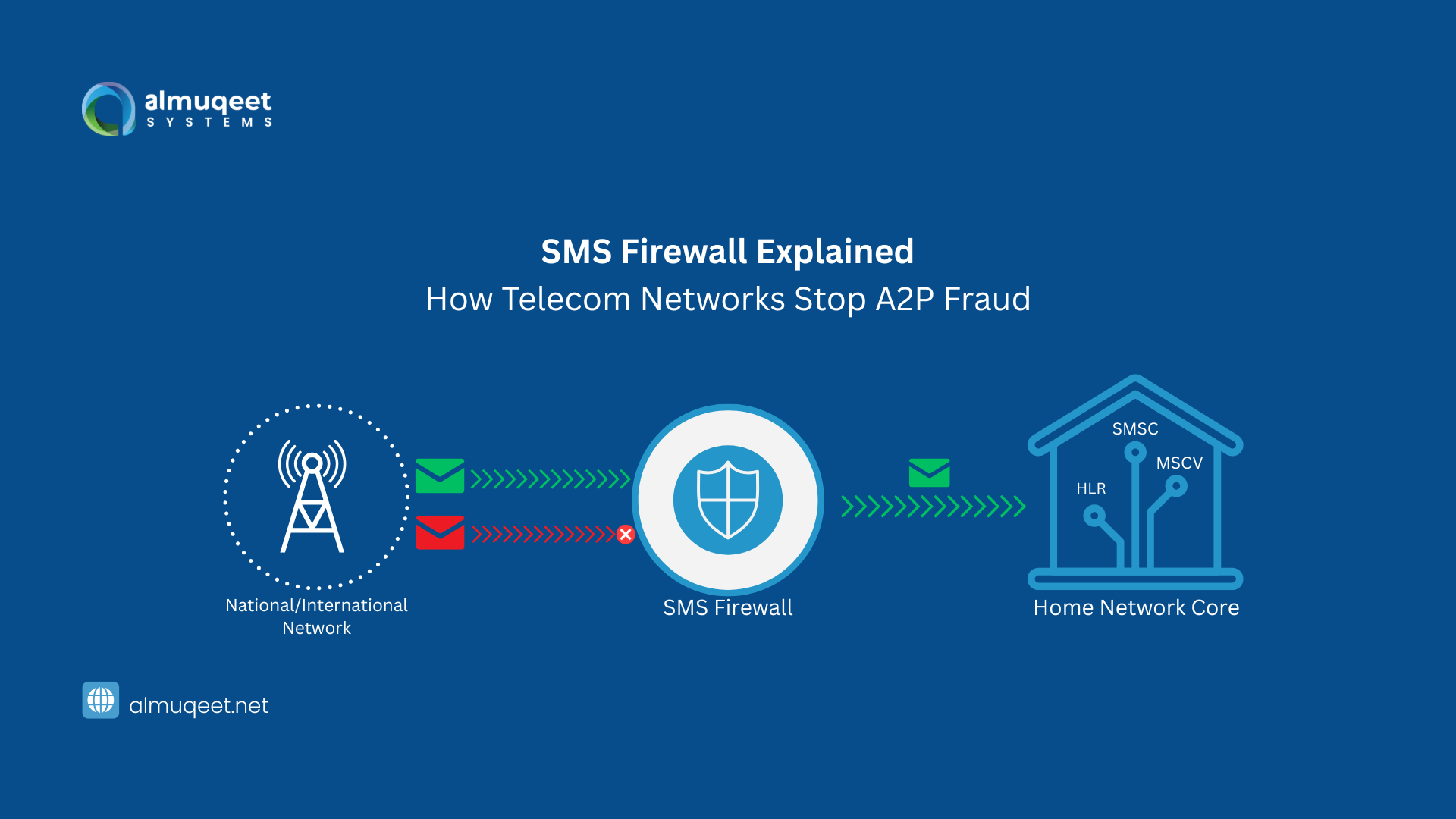
That loss of control is exactly why SMS firewall systems have become a standard part of modern telecom architecture. They aren’t just defensive tools. They act as a control layer that helps operators understand what is actually happening inside their messaging environment.
Understanding What an SMS Firewall Actually Does
At its core, an SMS firewall sits between the telecom signaling layer and the messaging traffic entering or leaving the network. Its role isn’t simply to block spam. That would be far too narrow. What it really does is inspect, classify, and control SMS traffic in real time.
Telecom networks were originally built for person-to-person communication. Over time, application-to-person messaging grew into something much larger. OTP verification, payment alerts, logistics updates, appointment reminders, millions of automated messages now flow through an infrastructure that wasn’t originally designed to distinguish them from normal texting behavior.
Without a firewall layer, the network sees only SMS packets moving through signaling routes. It cannot reliably determine:
- whether traffic originates from a legitimate enterprise platform
- whether messages are bypassing official routes
- whether international grey routes are injecting traffic into domestic networks
- whether sender IDs are being spoofed
An SMS firewall introduces that intelligence layer. It observes traffic patterns, analyzes signaling behavior, checks routing integrity, and enforces operator policies — all without interrupting legitimate communication. In practice, it’s less like a filter and more like an air-traffic controller for messaging networks.
Why SMS Firewalls Became Critical Infrastructure
Ten years ago, operators could tolerate some messaging irregularities. Grey routing existed, but the volume was manageable. That balance changed when A2P messaging exploded. Banks began sending authentication codes for every login. Ride-hailing platforms pushed real-time notifications. E-commerce systems started using SMS for order confirmations and delivery updates. Healthcare systems adopted messaging for appointment coordination.
Suddenly, what looked like ordinary SMS traffic became revenue-generating business communication. That shift introduced two problems at once. First, the value of A2P traffic increased dramatically. Second, attackers and bypass operators began targeting that revenue.
Grey routes started injecting enterprise traffic through international gateways to avoid operator fees. Fraudulent actors spoofed sender IDs to impersonate banks. Spam networks used compromised routes to push millions of unsolicited messages. At the same time, enterprise customers began demanding reliability.
A fintech company sending OTPs cannot tolerate delivery delays. A logistics platform cannot afford routing congestion during peak hours. For them, messaging performance is not cosmetic, it’s operational. This is where SMS firewall solutions became necessary. They provide operators with the visibility and enforcement mechanisms required to protect messaging revenue while maintaining service reliability.
What an SMS Firewall Monitors Inside a Telecom Network
A well-designed firewall operates quietly, but the number of signals it observes is enormous. Modern systems analyze traffic across multiple dimensions:
- Signaling behavior: monitoring SS7, Diameter, and SMPP interactions to detect abnormal routing patterns
- Traffic classification: distinguishing A2P, P2P, and hybrid messaging flows
- Sender identity verification: detecting spoofed or unauthorized sender IDs
- Routing path analysis: identifying grey routes attempting to bypass official messaging channels
Individually, none of these signals tells the full story. But when analyzed together, they reveal patterns operators would otherwise miss.
For example, a sudden spike in international signaling requests combined with identical sender IDs across multiple routes often indicates bypass traffic. Without a firewall, that pattern may remain invisible for weeks. With one, the system can block or redirect the traffic in seconds.
The Grey Route Problem Operators Quietly Fight
Grey routes remain one of the most persistent threats to telecom messaging revenue. They work because messaging networks are interconnected globally. Operators exchange traffic across multiple international gateways, and that complexity creates opportunities for bypass routing.
A grey route typically works like this, an enterprise sends A2P messages through a low-cost international aggregator rather than the operator’s authorized messaging platform. The traffic enters the destination country disguised as person-to-person SMS, avoiding termination fees. From the outside, the messages appear legitimate. They arrive on real devices. Delivery reports are generated.
But the operator loses revenue, and the network loses control over traffic quality. Over time, these bypass routes degrade the entire messaging ecosystem. Delivery reliability declines. Spam increases. Legitimate enterprise traffic competes with uncontrolled message flows. An SMS firewall identifies and blocks these routes by analyzing signaling behavior and routing paths before the messages reach subscribers.
When Messaging Infrastructure Faces Real Scale
Consider a large e-commerce platform during a regional sales event. Within a few minutes, millions of customers attempt logins, payment verifications, and order confirmations. Each action triggers SMS notifications. From the enterprise side, everything seems straightforward, an API sends messages to an aggregator, and the platform waits for delivery confirmations.
Inside the telecom network, the situation looks very different. Traffic surges through multiple SMSCs. International routes attempt to inject additional traffic. Some senders retry messages repeatedly when delivery reports lag. Network congestion builds around key signaling nodes.
This is the moment when a messaging firewall proves its value. Instead of treating all traffic equally, the system prioritizes legitimate A2P traffic, filters suspicious flows, and maintains routing stability. Without that control layer, congestion spreads quickly. OTPs arrive late. Customers retry authentication. Message volume doubles. The network begins chasing its own tail. Operators who’ve experienced this once rarely operate without a firewall afterward.
Where SMS Firewalls Fit in the Messaging Architecture
To understand their role properly, it helps to view messaging infrastructure as a layered system. At the base are signaling networks such as SS7 or Diameter, responsible for routing messages between telecom operators. Above that sits the SMSC layer, which stores, forwards, and manages message delivery.
Enterprise messaging platforms connect through SMPP gateways or APIs, injecting application-generated traffic into the network. The firewall sits between these layers, observing both signaling interactions and message flows. This position allows it to enforce policies across the entire messaging environment.
It can block unauthorized traffic before it reaches the SMSC. It can flag suspicious signaling requests. It can redirect messages through authorized routes. In many ways, it acts as the policy engine for telecom messaging networks. For readers exploring the broader architecture behind enterprise messaging systems, topics like SMS hubs and routing aggregation play a related role in controlling traffic flow across operator networks.
SMS Firewalls and Messaging Compliance
As messaging networks grew into financial and authentication infrastructure, regulators began paying closer attention. Financial institutions rely heavily on SMS for multi-factor authentication. Healthcare providers use messaging for patient communication. Governments use it for emergency alerts. These industries require traceability. Operators must demonstrate that messaging traffic is properly routed, monitored, and protected against abuse.
SMS firewalls help enforce these requirements by:
- logging traffic behavior
- verifying sender identity
- detecting spoofed messages that impersonate trusted brands
Without these controls, messaging networks become vulnerable not only to spam but also to large-scale fraud campaigns.
The Invisible Economics of Messaging Security
Many operators initially evaluate firewall deployments through a security lens. But the economics are often more compelling. Grey route filtering alone can recover significant messaging revenue by redirecting A2P traffic through authorized routes. Operators who deploy firewalls frequently discover how much traffic has been bypassing their networks unnoticed.
At the same time, enterprise messaging customers begin to see improved delivery reliability, which matters. A delayed OTP can break a financial transaction. A missing delivery notification can trigger customer support escalations. A spoofed sender ID can damage brand trust overnight. In messaging infrastructure, security and service quality are tightly connected.
Why Messaging Protection Will Matter Even More After 2026
Messaging is evolving again, rich messaging channels, verification services, and cross-channel communication platforms are pushing telecom networks into deeper integration with digital services. But despite these changes, SMS remains the most universal messaging layer on the planet.
No app installation required. No platform dependency. No device compatibility issues. That universality is exactly why the SMS firewall remains relevant. As long as SMS continues to carry authentication codes, transaction alerts, and critical notifications, telecom networks must maintain control over how those messages enter and move through the system.
Not aggressively, just carefully. Because messaging networks function best when their complexity stays mostly invisible to the people relying on them.
FAQs
What is an SMS firewall in telecom networks?
An SMS firewall is a security and traffic-management system used by telecom operators to monitor, filter, and control SMS traffic. It detects grey routes, spoofed sender IDs, spam campaigns, and unauthorized A2P traffic before messages reach subscribers.
Why do telecom operators deploy SMS firewalls?
Operators deploy SMS firewalls to protect messaging revenue, prevent routing bypass, reduce spam, and ensure reliable delivery for enterprise messaging traffic such as OTPs and transaction alerts.
How does an SMS firewall detect grey routes?
The system analyzes signaling behavior, routing paths, and sender identity patterns. When enterprise traffic enters through unauthorized international routes disguised as P2P messages, the firewall flags and blocks the traffic.
Can SMS firewalls affect message delivery speed?
When properly configured, they typically improve delivery performance. By filtering fraudulent or congested routes, the firewall ensures legitimate enterprise traffic moves through stable routing paths.
Are SMS firewalls only used for spam filtering?
No. Spam filtering is only one function. Modern SMS firewall solutions also protect telecom revenue, enforce messaging compliance, detect signaling attacks, and maintain overall network integrity.
Do enterprise messaging platforms interact with SMS firewalls?
Indirectly, yes. When enterprises send messages through official messaging gateways or SMS platforms, the traffic passes through operator firewalls that verify routing integrity and sender authenticity.
